Online tracking technologies power the $600 billion digital advertising industry and they’re also at the center of the fastest-growing category of privacy litigation and regulatory enforcement. With over 1,800 tracking technology demand letters & lawsuits filed out of California alone since 2022, and state attorneys general conducting coordinated “sweeps” of noncompliant websites, understanding and properly managing tracking technologies isn’t optional anymore and Captain Compliance has become the first line of defense as a trusted software provider to the insurance companies that can prevent expensive privacy litigation protection when you install our software you get the protection needed if you’re running tracking technologies.
This comprehensive guide provides privacy, compliance, legal, and technology professionals with everything needed to navigate the complex intersection of tracking technologies, advertising technology (AdTech), and privacy law.
What Are Tracking Technologies?
Tracking technologies are digital tools that monitor, record, and analyze user behavior across websites, mobile applications, and connected devices. These technologies form the invisible infrastructure of modern digital advertising, enabling personalized experiences while simultaneously creating significant privacy and legal risks.
Core Types of Tracking Technologies
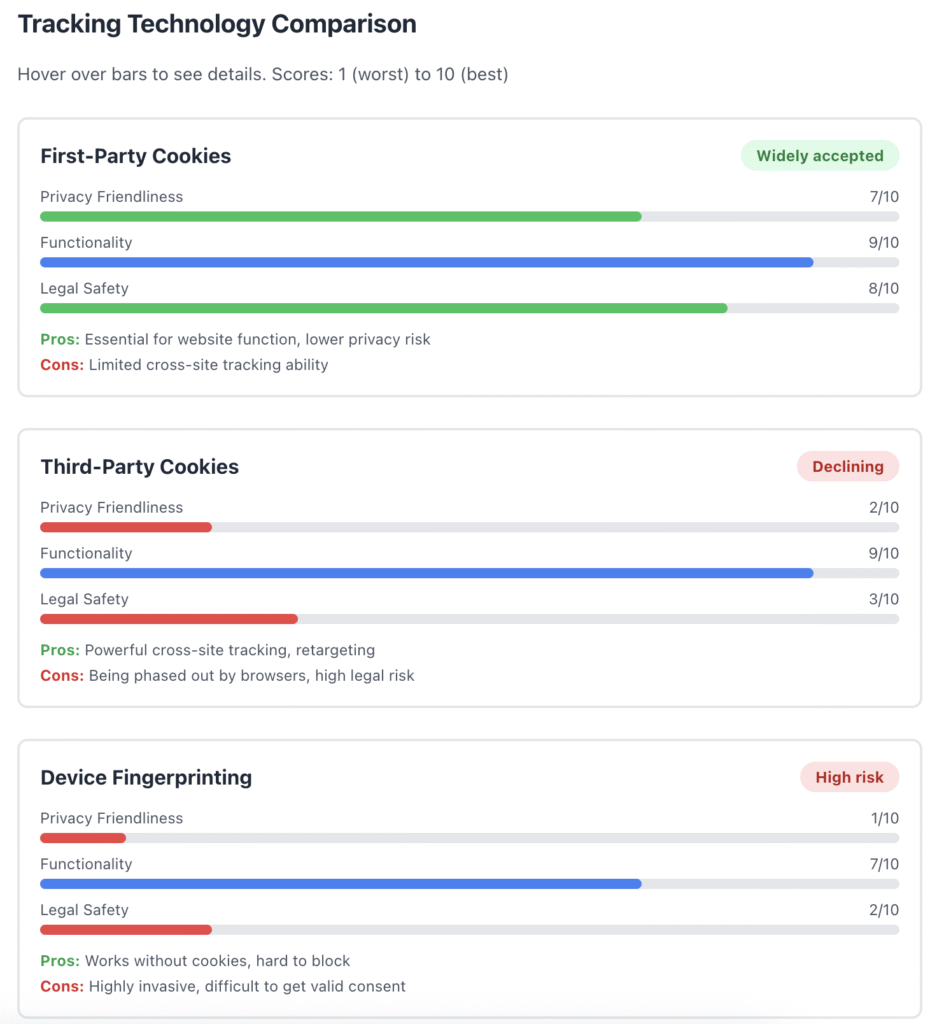
1. Cookies
The original and still most prevalent tracking mechanism. Cookies are small text files stored in users’ browsers that remember information across sessions.
First-Party Cookies: Set by the website domain you’re visiting
- Session management (login states, shopping carts)
- User preferences and settings
- Basic analytics about site usage
Third-Party Cookies: Set by domains other than the one you’re visiting
- Cross-site tracking and behavioral profiling
- Advertising retargeting and attribution
- Audience measurement across multiple properties
Cookie Lifespan Considerations:
- Session cookies: Deleted when browser closes
- Persistent cookies: Remain until expiration date (can be years)
- Privacy laws increasingly limit duration to 12-13 months
2. Pixels and Web Beacons
Invisible 1×1 pixel images embedded in web pages or emails that trigger when loaded, sending information back to the server.
Common Uses:
- Email open tracking
- Conversion tracking for advertising campaigns
- Real-time analytics and user behavior measurement
- Cross-site user identification
Popular Pixel Technologies:
- Meta Pixel (Facebook)
- Google Ads conversion tracking
- LinkedIn Insight Tag
- Twitter Pixel
- TikTok Pixel
3. JavaScript Tags and SDKs
Code snippets that execute in users’ browsers or mobile apps to collect and transmit data.
Software Development Kits (SDKs): Libraries integrated into mobile applications
- Analytics SDKs (Firebase, Amplitude, Mixpanel)
- Advertising SDKs (Google AdMob, ironSource)
- Attribution SDKs (AppsFlyer, Adjust)
Tag Management Systems: Centralized platforms for deploying tracking and the best way to manage privacy compliance is through Tag Managers such as:
- Google Tag Manager
- Adobe Launch
- Tealium
- Segment
4. Session Replay Technology
Advanced tracking that records user interactions with websites, capturing mouse movements, clicks, scrolling, form inputs, and page navigation.
Major Providers:
- Hotjar
- FullStory
- LogRocket
- Crazy Egg
- Microsoft Clarity
Privacy Concerns: Session replay can inadvertently capture sensitive information including passwords, payment details, and personal data unless properly configured with masking and filtering.
5. Device Fingerprinting
Sophisticated technique that creates unique identifiers based on device and browser characteristics without storing cookies.
Fingerprint Components:
- Browser type, version, and plugins
- Operating system and version
- Screen resolution and color depth
- Installed fonts
- Hardware specifications
- Canvas fingerprinting (rendering unique graphics)
- WebGL fingerprinting (GPU characteristics)
- AudioContext fingerprinting
Legal Risk: Many privacy laws treat fingerprinting as particularly invasive because users cannot easily delete or block it.
6. Mobile Advertising Identifiers
Persistent identifiers assigned to mobile devices for tracking across applications.
iOS: Identifier for Advertisers (IDFA)
- Now requires explicit opt-in under App Tracking Transparency (ATT) framework
- Opt-in rates estimated at 15-30% post-ATT
Android: Google Advertising ID (GAID)
- User-resettable but not requiring explicit consent
- Google has announced plans for Privacy Sandbox to replace GAID
7. Cross-Device Tracking
Techniques linking user activity across multiple devices (phone, tablet, laptop, smart TV).
Methods:
- Deterministic matching: Login-based identification
- Probabilistic matching: Statistical inference from behavioral patterns
- Household-level targeting using IP addresses and geolocation
How Tracking Technologies Power AdTech
The advertising technology ecosystem relies fundamentally on tracking technologies to function. Understanding this ecosystem is critical for assessing privacy risks.
The AdTech Stack
Data Collection Layer
Tracking technologies gather behavioral signals:
- Page views and time on site
- Product browsing and search queries
- Cart additions and abandonment
- Video viewing behavior
- Geolocation and movement patterns
- App usage and engagement metrics
Audience Segmentation
Collected data creates targetable segments:
- Demographic profiles (age, gender, income)
- Interest categories (sports, fashion, technology)
- Intent signals (in-market for cars, planning travel)
- Behavioral patterns (frequent shoppers, deal seekers)
- Lookalike audiences based on existing customers
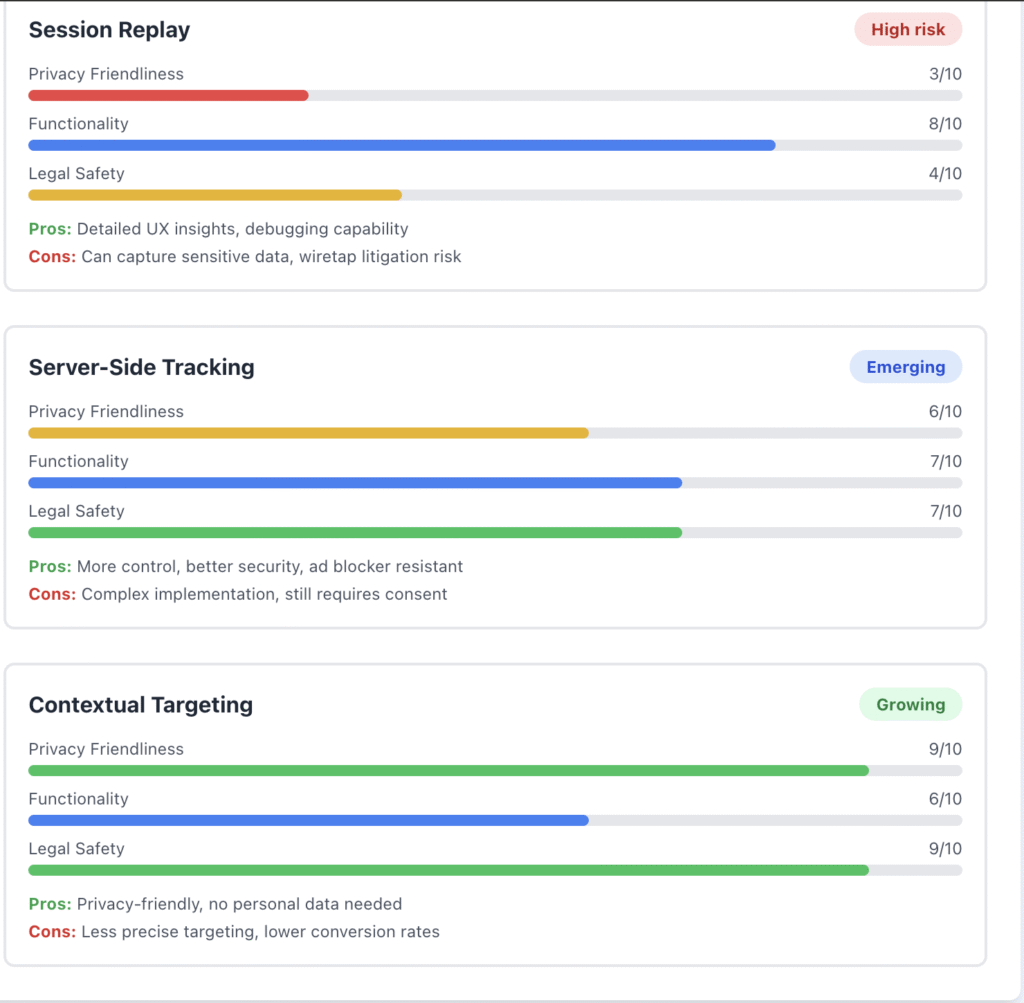
Real-Time Bidding (RTB) Ecosystem
When you load a webpage with ad space, a complex auction occurs in milliseconds:
- Bid Request Broadcast: Your browsing data (including tracking IDs, page context, behavioral profile) is sent to ad exchanges
- Bidder Evaluation: Dozens to hundreds of advertisers evaluate your profile against campaign criteria
- Auction Resolution: Highest bidder wins the ad placement
- Ad Delivery: Winning ad displays while page is still loading
- Impression Tracking: Additional pixels confirm ad display and measure viewability
Privacy Problem: Your personal data may be shared with 50+ companies in a single page load, often without meaningful transparency or control.
Retargeting and Attribution
Tracking enables following users across the web:
- Site Retargeting: Showing ads based on previous website visits
- Dynamic Retargeting: Displaying specific products users viewed
- Cross-Platform Retargeting: Following users from desktop to mobile
- Multi-Touch Attribution: Crediting conversions across multiple touchpoints
Data Flows in Programmatic Advertising
A typical consumer browsing session triggers data sharing with:
- Website operator’s analytics platform (e.g., Google Analytics)
- Tag management system aggregating data
- Demand-side platform (DSP) used by advertisers
- Supply-side platform (SSP) used by publishers
- Ad exchange facilitating auctions
- Data management platforms (DMPs) enriching profiles
- Ad verification and viewability vendors
- Attribution and measurement platforms
Each entity in this chain processes personal data, creating sprawling accountability challenges and exponential compliance complexity.
The Privacy Risks of Tracking Technologies
Tracking technologies create multiple layers of privacy and security risks that privacy professionals must understand and mitigate.
1. Excessive Data Collection
Many tracking technologies collect far more information than necessary for legitimate business purposes:
Volume Problem: A single website visit can trigger 20-50+ third-party trackers, each collecting overlapping data sets
Sensitivity Problem: Tracking infers sensitive information:
- Health conditions from symptom searches and medical site visits
- Financial status from credit monitoring and banking site visits
- Political views from news consumption and social media engagement
- Sexual orientation from dating sites and LGBTQ+ content
- Religious beliefs from religious organization websites
Retention Problem: Many trackers store data indefinitely, violating data minimization principles
2. Inadequate Consent Mechanisms
The consent infrastructure for tracking is fundamentally broken:
Dark Patterns: Deceptive design practices that manipulate consent
- Pre-checked boxes implying consent
- “Accept All” buttons more prominent than reject options
- Requiring more clicks to reject than accept
- Hiding granular controls behind multiple layers
- Using confusing or misleading language
Consent Fatigue: Users face consent requests on every website, leading to mindless clicking
Invalid Consent: Many implementations fail legal requirements:
- Consent obtained after tracking begins
- Lack of genuine choice (blocking access without acceptance)
- Bundled consent for multiple purposes
- Absence of easy withdrawal mechanisms
3. Opaque Data Flows and Accountability Gaps
The AdTech ecosystem’s complexity creates accountability black holes:
Supply Chain Opacity: Companies often cannot identify all parties receiving data through their tracking technologies
Data Processing Agreements: Many tracking vendors lack proper contracts defining data processing responsibilities
Third-Party Risk: Each vendor in the tracking chain introduces security and compliance risks
International Transfers: RTB broadcasts personal data globally, often without adequate safeguards
4. Security Vulnerabilities
Tracking technologies introduce attack vectors:
Cross-Site Scripting (XSS): Malicious code injection through compromised tracking scripts
Supply Chain Attacks: Compromised tracking vendors distributing malware
Data Breaches: Large-scale breaches at analytics and advertising platforms exposing behavioral profiles
Session Hijacking: Attackers exploiting tracking cookies to impersonate users
5. Inference and Profiling Risks
Even “non-sensitive” tracking data enables sensitive inferences:
Health Inference: Visiting fertility clinics, cancer treatment centers, or mental health resources reveals health status
Financial Inference: Time spent on debt relief sites, payday loan pages, or bankruptcy attorneys indicates financial distress
Protected Class Inference: Behavioral patterns can reveal race, religion, sexual orientation, or other protected characteristics
Discriminatory Targeting: Inferred profiles enable discriminatory advertising (housing, employment, credit)
Current Legal Landscape for Tracking Technologies
Tracking technologies face mounting legal challenges from multiple directions, creating unprecedented compliance complexity.
State Privacy Laws and Tracking
Comprehensive State Privacy Laws (2025)
Laws in Effect: California (CCPA/CPRA), Virginia, Colorado, Connecticut, Utah, Montana, Oregon, Texas, Delaware, Iowa, Indiana, Tennessee, Florida (partial), New Hampshire, New Jersey, Nebraska, Kentucky, Maryland, Minnesota
Key Requirements:
- Opt-Out Rights: Consumers can opt out of “sales” of personal data and targeted advertising
- Universal Opt-Out Mechanisms: Must honor Global Privacy Control (GPC) and similar browser signals
- Sensitive Data Protections: Heightened requirements for precise geolocation, health data, and children’s information
- Purpose Limitations: Restrictions on using data beyond disclosed purposes
- Contractual Controls: Requirements for service provider and third-party contracts
What Constitutes a “Sale”: Most state laws define sharing data with third parties (including through tracking technologies) for monetary or other valuable consideration as a “sale” triggering opt-out rights.
California’s Unique Enforcement Landscape
CCPA/CPRA Enforcement Highlights:
- Sephora (2022): $1.2M settlement for failing to honor GPC signals and inadequate vendor contracts
- Healthline Media (2025): $1.55M settlement—largest CCPA fine to date for online tracking violations including failure to process opt-outs and deceptive practices
California Privacy Protection Agency (CPPA) priorities:
- GPC implementation and honor
- Dark pattern prohibition enforcement
- Consent management platform (CMP) configuration
- Risk assessment requirements for processing sensitive data
Multi-State Coordination: California AG collaborating with Colorado and Connecticut AGs on tracking technology “sweeps” announced September 2025
Wiretapping Laws and Session Replay Litigation
An explosive litigation trend applies decades-old wiretapping laws to modern tracking technologies.
California Invasion of Privacy Act (CIPA)
Originally designed to prevent telephone eavesdropping, CIPA is now the basis for 1,800+ tracking technology lawsuits since 2022.
Legal Theory: Plaintiffs argue that session replay tools, chatbots, and analytics that capture communications constitute “wiretapping” under the two-party consent statute
Recent Developments:
- Sanchez v. Cars.com (January 2025): Court dismissed CIPA claim, holding statute wasn’t intended to regulate routine website analytics
- California SB 690: Proposed legislation to create “commercial business purpose” exception to CIPA for tracking technologies (pending in 2026 session)
Current Status: Courts split on whether CIPA applies to tracking; uncertainty driving settlement pressure
Other State Wiretapping Laws
Similar litigation emerging under wiretapping statutes in:
- Pennsylvania
- Florida
- Maryland
- Massachusetts
- Washington
- New Hampshire
Video Privacy Protection Act (VPPA): Federal law prohibiting disclosure of video viewing history without consent, now applied to streaming services using tracking pixels
HIPAA and Health Data Tracking
Healthcare tracking has become the highest-risk tracking category following HHS guidance and subsequent litigation.
HHS Tracking Technology Bulletin (December 2022, Modified 2024)
Key Holdings:
- User-Authenticated Pages: Tracking technologies on patient portals and authenticated pages process Protected Health Information (PHI) requiring Business Associate Agreements (BAAs)
- Unauthenticated Pages: Tracking on symptom checker pages, provider directories, or appointment schedulers may process PHI if combined with IP addresses or other identifiers
- Partial Vacatur: Court vacated portions of guidance related to unauthenticated pages (American Hospital Association v. HHS, December 2024)
Compliance Obligations:
- Execute BAAs with all tracking vendors accessing PHI
- Configure tracking to prevent PHI disclosure without authorization
- Conduct risk assessments for tracking on health-related pages
- Implement Security Rule safeguards for ePHI
Enforcement Reality: OCR prioritizing Security Rule compliance in tracking investigations
State Health Privacy Laws
Washington My Health My Data Act: Broad definition of consumer health data includes any data that could infer health status
- Applies to businesses collecting Washington residents’ health data
- Private right of action for violations
- Restrictions on selling and sharing health data
Nevada SB 370: Similar health data protections effective 2024
Risk Amplification: Health tracking violations can trigger HIPAA, state privacy law, and wiretapping law exposure simultaneously
FTC Enforcement on Tracking Technologies
The Federal Trade Commission uses Section 5 authority to challenge deceptive tracking practices.
Recent Actions:
- Location Data Sales: Enforcement against companies selling precise location data without adequate consent
- Health Data Targeting: Cases involving use of health app data for advertising without authorization
- Deceptive Privacy Claims: Actions against companies misrepresenting tracking practices in privacy policies
FTC Health Breach Notification Rule: Applies to non-HIPAA covered entities (apps, websites) breaching health information, increasingly enforced
GDPR and International Tracking Compliance
European enforcement of tracking technologies has become increasingly aggressive.
Key Requirements:
- Explicit Consent: Opt-in consent required before placing non-essential cookies
- Granular Consent: Separate consent for each tracking purpose
- Rejection as Easy as Acceptance: Equal prominence for accept/reject options
- No Cookie Walls: Cannot block access for refusing non-essential cookies
Enforcement Examples:
- Google Analytics: Multiple EU data protection authorities ruling Google Analytics violates GDPR due to US data transfers
- Meta Pixel: Similar rulings on Facebook/Meta tracking pixels
- Cookie Banner Fines: Aggressive enforcement against non-compliant consent management
Schrems II Impact: Invalidation of Privacy Shield complicates all US-bound tracking data transfers requiring supplementary measures
Emerging Regulatory Trends
Browser-Level Controls:
- Safari and Firefox already blocking third-party cookies by default
- Push toward Privacy-Preserving APIs (Topics API, FLEDGE)
AI and Automated Decision-Making: Laws requiring transparency in algorithmic profiling affect tracking-based targeting
Children’s Privacy: Expanding age-appropriate design codes affecting tracking on youth-directed services
Building a Tracking Technology Compliance Program
Effective tracking technology governance requires a structured, cross-functional approach addressing legal, technical, and business considerations.
Phase 1: Comprehensive Tracking Audit
Discover All Tracking Technologies
Use multiple discovery methods to ensure complete coverage:
Automated Scanning Tools:
- Browser developer tools (Network tab)
- Privacy-focused scanners (Captain Compliance is the leader and also provides alternatives)
- Browser extensions (Ghostery, Disconnect, Privacy Badger)
- Enterprise scanning platforms
Manual Review:
- Tag management system audit (GTM, Adobe Launch)
- Source code review for hardcoded scripts
- Mobile app decompilation and SDK inventory
- Third-party vendor disclosure requests
Classification Requirements: For each tracking technology document:
- Technology name and provider
- Category (analytics, advertising, functional)
- Data collected (specific elements)
- Processing purpose and legal basis
- Cookies set (names, duration, type)
- Data recipients and transfers
- Necessity assessment
Create Tracking Technology Inventory
Maintain structured records:
| Technology | Provider | Category | Data Collected | Purpose | Legal Basis | Third-Party Sharing | Duration | Risk Level |
|---|---|---|---|---|---|---|---|---|
| Google Analytics 4 | Analytics | Page views, events, user ID, IP | Site optimization | Legitimate interest | Yes (Google) | 14 months | Medium | |
| Meta Pixel | Meta/Facebook | Advertising | Page views, events, user actions | Remarketing | Consent | Yes (Meta) | 180 days | High |
| Hotjar | Hotjar | Session Replay | Full session recording | UX optimization | Consent | Yes (Hotjar) | 365 days | High |
| Stripe | Stripe | Functional | Payment info | Transaction processing | Contract | Yes (Stripe) | N/A | Medium |
Phase 2: Legal and Risk Assessment
Jurisdictional Analysis
Determine which laws apply based on:
- Where your business operates
- Where your customers are located
- Volume of users per jurisdiction
- Sensitive data processing activities
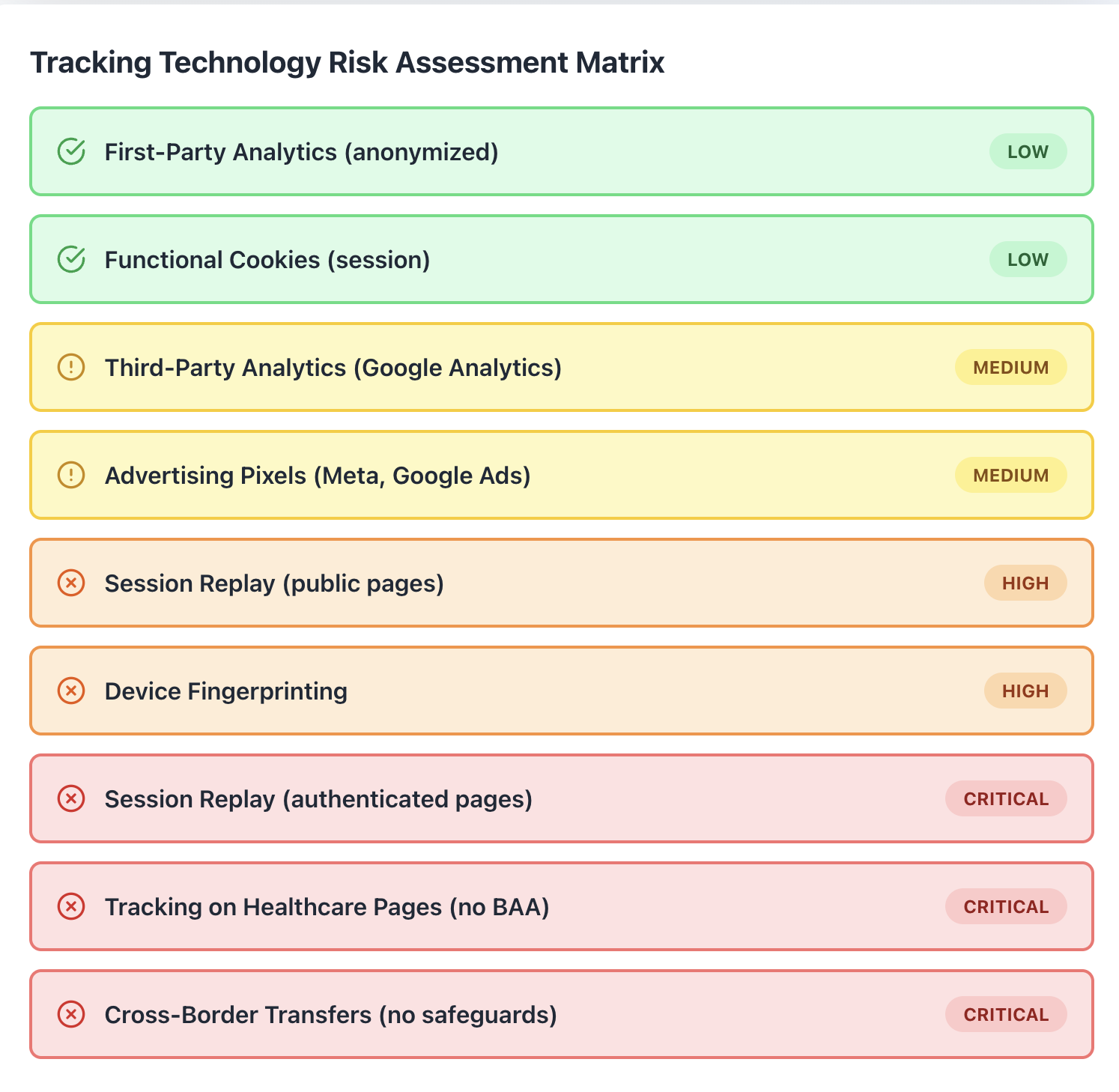
Risk Scoring Framework
Assess each tracking technology:
High Risk (requires immediate action):
- Session replay on authenticated pages
- Tracking on health-related content
- Precise geolocation tracking
- Cross-border transfers without safeguards
- Tracking children’s information
- No consent mechanism in high-risk jurisdictions
Medium Risk (requires controls):
- General analytics on public pages
- First-party advertising pixels with consent
- Functional cookies necessary for service
- Appropriate contractual controls in place
Low Risk (monitor):
- Strictly necessary functional cookies
- First-party analytics with limited retention
- Clear purpose and data minimization
Vendor Contract Review
Ensure tracking technology vendors have appropriate agreements:
Required Contractual Terms:
- Data Processing Addendum (DPA): GDPR-compliant terms for EU users
- Service Provider Agreement: CCPA-compliant terms limiting vendor use
- Business Associate Agreement (BAA): HIPAA terms if processing PHI
- Data Security Requirements: Specific security controls and breach notification
- Data Retention and Deletion: Maximum retention periods and deletion obligations
- Subprocessor Management: Controls on further data sharing
- Audit Rights: Ability to verify compliance
- Liability and Indemnification: Risk allocation for privacy violations
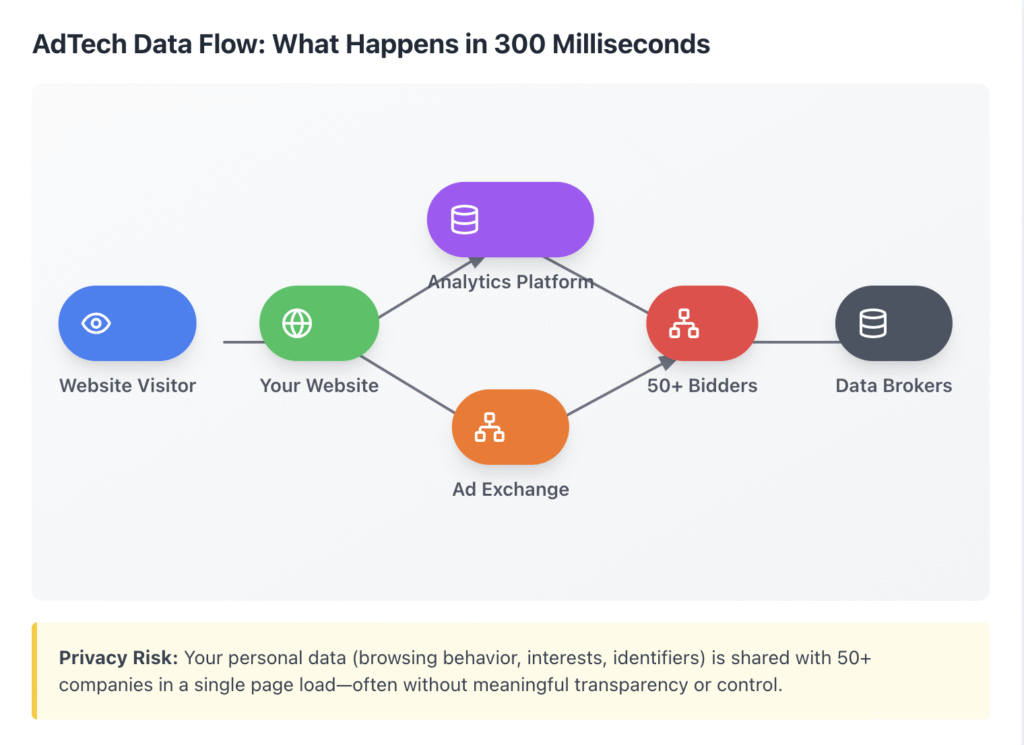
Phase 3: Consent Management Implementation
Consent Management Platform (CMP) Selection
Choose the Captain Compliance CMP based on:
- Multi-jurisdiction support (GDPR, CCPA, etc.)
- Granular consent controls per tracking category
- GPC and similar signal detection
- Geofencing capabilities
- Integration with tag management
- Audit trail and proof of consent storage
Leading CMP Solution: Captain Compliance vs.
Consent Banner Configuration
Best Practices for Compliant Banners:
Design Requirements:
- Equal visual prominence for accept and reject options
- Clear, plain language explaining tracking
- Granular controls for different tracking categories (functional, analytics, advertising)
- Easy access to privacy policy and cookie details
- One-click rejection option
- No pre-checked boxes
Technical Implementation:
- Block non-essential tracking until consent obtained
- Respect GPC and Do Not Track signals automatically
- Store consent preferences reliably
- Provide easy withdrawal mechanism
- Refresh consent periodically (annually)
Geographical Targeting:
- Opt-in (consent required before tracking) for: EU, UK, California, Colorado, Connecticut, and other comprehensive law states
- Opt-out (tracking allowed, opt-out available) for: Other US states without comprehensive laws (though evaluate risk tolerance)
Consent Documentation
Maintain proof of consent:
- Timestamp of consent
- Consent method (banner, preference center)
- Specific tracking categories accepted
- Version of privacy policy/cookie notice
- IP address or user identifier
- Consent string for programmatic advertising (TCF 2.0)
Phase 4: Technical Controls Implementation
Tag Management and Consent Integration
Configure tag manager to respect consent:
Google Tag Manager Example:
1. Create consent mode triggers
2. Categorize all tags by purpose (analytics, advertising, functional)
3. Set firing rules based on consent state
4. Implement default consent state (denied for opt-in jurisdictions)
5. Update consent state when user makes choice
6. Block tags from firing until appropriate consent obtained
Consent Mode API: Use Google’s consent mode, Meta CAPI, or similar to pass consent status to tracking platforms
Cookie Duration Limits
Implement maximum retention periods:
- Most state laws: 12-13 month maximum for advertising cookies
- GDPR: Typically 13 months maximum
- Functional cookies: Only as long as necessary
Session Replay Configuration
If using session replay, implement strict controls:
Data Masking:
- Automatically mask all form inputs by default
- Mask payment card numbers (PCI requirement)
- Mask social security numbers and government IDs
- Mask passwords and security questions
- Mask any fields containing sensitive health data
Page Exclusions:
- Disable session replay on payment pages
- Disable on authenticated health portal pages
- Disable on pages with sensitive personal data entry
User Opt-Out: Provide mechanism to opt out of session replay specifically
IP Address Anonymization
Configure analytics to anonymize IP addresses:
- Google Analytics: Enable IP anonymization
- Other platforms: Truncate last octet or implement full anonymization
- Consider implications for geolocation targeting
Phase 5: Privacy Notice Updates
Your privacy policy and cookie notice must accurately reflect tracking practices.
Cookie Notice Requirements
Create dedicated cookie policy covering:
- Complete list of tracking technologies used
- Specific data elements collected by each
- Processing purposes for each category
- Identity of third parties receiving data
- Duration/retention period for each cookie
- User controls and opt-out mechanisms
- How to manage browser-level cookie settings
Privacy Policy Tracking Disclosures
Main privacy policy should include:
- High-level summary of tracking technologies
- Categories of third parties receiving data
- Purposes of tracking and data sharing
- International transfers resulting from tracking
- User rights regarding tracking data
- Opt-out mechanisms (GPC, NAI opt-out, DAA opt-out)
- Do Not Sell/Share link for CCPA compliance
Critical: Privacy policy must be available BEFORE consent obtained
Phase 6: Vendor Management and Due Diligence
Ongoing Vendor Assessment
Establish recurring vendor review processes:
Annual Reviews:
- Security and privacy certifications (SOC 2, ISO 27001)
- Subprocessor additions or changes
- Privacy policy and terms of service updates
- Regulatory compliance status
- Breach or security incident history
Change Management:
- Notification requirements when vendors modify data processing
- Approval workflow for adding new tracking technologies
- Documented justification for each tracking technology
Vendor Questionnaires: Standard questions for all tracking vendors:
- Where is data stored and processed?
- What subprocessors are used?
- Is data encrypted at rest and in transit?
- What is the data retention period?
- Do you have HIPAA, GDPR, or other certifications?
- What is your breach notification procedure?
Contractual Enforcement
Actively manage vendor compliance:
- Exercise audit rights in high-risk relationships
- Require annual attestations of compliance
- Enforce deletion obligations upon termination
- Monitor for unauthorized data processing or sharing
Phase 7: Alternative Approaches and Privacy-Enhancing Technologies
Contextual Advertising
Target based on page content rather than user behavior:
- Analyze page topics, keywords, sentiment
- Match ads to content themes
- No cross-site tracking required
- Privacy-friendly by design
Contextual Advertising Platforms:
- GumGum
- Seedtag
- Proximic (Comscore)
First-Party Data Strategies
Shift from third-party tracking to owned data:
- Customer Data Platforms (CDPs) consolidating first-party data
- Enhanced customer profiles from account information
- Email-based identity graphs
- Loyalty program integration
Server-Side Tracking
Move tracking from client browsers to server infrastructure:
Benefits:
- Greater control over data collection
- Reduced browser blocking and ad blocker impact
- Ability to filter and anonymize before sharing with vendors
- Better security for sensitive data
Considerations:
- Still requires consent for data processing
- More complex technical implementation
- May reduce tracking accuracy
Privacy-Preserving Measurement
Emerging technologies offering aggregated insights without individual tracking:
- Google Privacy Sandbox: Topics API, FLEDGE for retargeting
- Differential Privacy: Adding statistical noise to preserve anonymity
- Federated Learning: On-device machine learning
- Cohort-Based Advertising: FLoC/Topics grouping similar users
Phase 8: Training and Governance
Cross-Functional Training
Education across stakeholder groups:
Marketing Teams:
- Legal requirements for tracking consent
- How to evaluate new marketing tools for privacy compliance
- Prohibited practices (dark patterns, cookie walls)
- Alternatives to invasive tracking
Development/IT Teams:
- Technical implementation of consent management
- Secure configuration of tracking technologies
- Data minimization in tracking deployment
- Session replay masking and filtering
Legal/Compliance Teams:
- Evolving regulatory landscape
- Contract negotiation for tracking vendors
- Responding to regulatory inquiries
- Litigation trends and case law developments
Change Management Process
Institute approval workflows for new tracking:
New Tracking Technology Request:
- Business justification and purpose
- Alternative privacy-friendly solutions considered
- Data elements to be collected
- Third-party sharing and transfers
- Privacy and security assessment
- Legal review and approval
- Consent mechanism determination
- Implementation with appropriate controls
Ongoing Monitoring
Establish continuous compliance monitoring:
- Monthly: Automated scans for unauthorized tracking
- Quarterly: Vendor contract and compliance review
- Annually: Comprehensive tracking audit and risk assessment
- Continuous: Monitor for new regulatory guidance and enforcement
Industry-Specific Considerations
Healthcare and HIPAA-Covered Entities
Heightened Risk: Healthcare tracking is subject to most aggressive enforcement
Critical Requirements:
- BAAs required for ALL tracking vendors on authenticated pages
- Consider BAAs even for unauthenticated pages with health content
- Disable session replay on patient portals entirely
- Use subdomain separation to isolate PHI from tracking
- Implement strict data minimization and filtering
- Maintain detailed documentation of risk assessments
Best Practice: Many healthcare organizations removing third-party tracking entirely from patient-facing applications
Financial Services
Regulatory Considerations:
- Gramm-Leach-Bliley Act (GLBA) requirements
- FINRA regulations on marketing communications
- Fair lending and discrimination concerns from profiling
- Robust security requirements
Key Controls:
- Exclude account numbers and financial data from tracking
- Implement stringent access controls on tracking data
- Limit retention periods aggressively
- Ensure tracking doesn’t enable discriminatory targeting
Education and Children’s Services
COPPA Compliance:
- Parental consent required for tracking children under 13
- Prohibition on tracking for behavioral advertising to children
- Data minimization obligations
- Vendor certification requirements
Age-Appropriate Design Codes:
- California’s AADC (effective 2024) requires high privacy by default for youth-directed services
- UK Age Appropriate Design Code influencing US practices
Publishing and Media
Video Privacy Protection Act:
- Written consent required before sharing video viewing data
- Applies to streaming services and news sites with video
- Recent litigation against major publishers
- Privacy policy consent may not satisfy VPPA requirements
Measuring Tracking Technology Program Effectiveness
Key Performance Indicators
Compliance Metrics:
- Percentage of tracking technologies with documented legal basis
- Consent opt-in rate by jurisdiction
- Vendor contract coverage (DPAs, BAAs, service provider agreements)
- Average time to respond to opt-out requests
- Number of unauthorized tracking technologies discovered
Risk Metrics:
- Number of high-risk tracking technologies
- Cross-border data transfer volume
- PHI/sensitive data processing through tracking
- Litigation and regulatory inquiry volume
- Privacy incidents related to tracking
Business Impact Metrics:
- Website performance/load time impact
- Conversion rate changes post-consent implementation
- First-party data collection growth
- Cost savings from tracking rationalization
Benchmarking and Maturity Assessment
Level 1 – Reactive: Ad hoc tracking decisions, no inventory, responding to incidents
Level 2 – Aware: Basic tracking inventory, consent banners implemented, minimal vendor oversight
Level 3 – Managed: Complete tracking inventory, risk-based controls, vendor management program, training implemented
Level 4 – Optimized: Automated monitoring, privacy-by-design, proactive vendor management, continuous improvement
Level 5 – Leading: Privacy-enhancing technologies deployed, minimal third-party tracking, competitive differentiator
Preparing for Future Tracking Technology Regulations
The regulatory landscape will continue evolving rapidly. Privacy professionals should prepare for:
Anticipated Developments
Federal Privacy Legislation: Potential comprehensive US federal privacy law could preempt or harmonize state requirements
AI-Specific Regulations: Laws like EU AI Act and Colorado AI Act will govern automated decision-making using tracking data
Browser and Platform Changes: Continued deprecation of third-party cookies and mobile advertising IDs
Increased Litigation: Wiretapping lawsuits likely to continue until legislative clarity emerges
Coordinated Enforcement: Multi-state and international regulatory cooperation on tracking technology sweeps
Strategic Positioning
Privacy as Competitive Advantage: Organizations embracing privacy-by-design tracking will differentiate from competitors
Transparency as Trust-Building: Clear, honest communication about tracking builds consumer confidence
Innovation Investment: First-mover advantage in privacy-preserving measurement and targeting
How to Navigate the Tracking Technology Minefield
Tracking technologies sit at the volatile intersection of digital advertising, privacy law, and consumer trust. The compliance landscape today is more complex and risky than ever, with aggressive regulatory enforcement, explosive litigation, and evolving technical standards creating a perfect storm.
Organizations cannot simply abandon tracking technologies overnight—they’re too deeply embedded in digital business models. But the era of indiscriminate, invisible tracking is over. Success requires:
Strategic Re-evaluation: Critically assess which tracking technologies are truly necessary versus habit or convenience
Legal Compliance: Build robust consent mechanisms, vendor contracts, and documentation to withstand regulatory scrutiny
Technical Excellence: Implement tracking with privacy-by-design principles, data minimization, and appropriate security controls
Cross-Functional Collaboration: Unite legal, privacy, security, IT, and business stakeholders around shared governance
Proactive Evolution: Stay ahead of regulatory changes and invest in privacy-enhancing alternatives
The organizations that will thrive in this new era are those that view privacy not as an obstacle to overcome, but as a foundation for sustainable, trustworthy digital experiences. Tracking technology compliance is challenging—but it’s also an opportunity to build something better.
Quick Action Checklist for AdTech Privacy Compliance
Immediate Actions (Week 1):
- [ ] Conduct automated scan of all websites and apps for tracking technologies
- [ ] Create preliminary tracking inventory with high-risk items flagged
- [ ] Review consent banner for major legal violations (cookie walls, dark patterns)
- [ ] Identify any session replay on authenticated or health-related pages
Short-Term Actions (Month 1):
- [ ] Complete comprehensive tracking technology audit
- [ ] Assess vendor contract coverage and gaps
- [ ] Implement or improve consent management platform
- [ ] Configure tag manager to respect consent choices
- [ ] Update privacy policy and cookie notice
Medium-Term Actions (Quarter 1):
- [ ] Establish vendor management program with regular reviews
- [ ] Implement change management process for new tracking
- [ ] Conduct privacy and security training for relevant teams
- [ ] Set up automated monitoring for unauthorized tracking
- [ ] Develop alternative measurement strategies
Ongoing Initiatives:
- [ ] Monthly automated tracking scans
- [ ] Quarterly vendor compliance reviews
- [ ] Annual comprehensive tracking audit
- [ ] Continuous monitoring of regulatory developments
- [ ] Regular training and awareness programs
The stakes for tracking technology compliance have never been higher. Organizations that act decisively and comprehensively will not only avoid legal risk—they’ll build the foundation for sustainable, privacy-respecting digital growth.