Now that a federal court just blew open the CCPA’s private right of action that we’ve been warning about for the last year you should know that your tracking pixels are in the crosshairs. The March 27 ruling in Allison v. PHH Mortgage rejects the narrow “data breach only” reading that businesses have relied on for years. What it means for every company running third-party trackers without proper consent architecture is not subtle.
Since the California Consumer Privacy Act took effect in 2020, the conventional wisdom around its private right of action has held a relatively comfortable shape for businesses. Yes, the CCPA gave California consumers the right to sue — but that right was widely understood to be tethered to a specific scenario: a traditional data breach, where a company’s inadequate security allowed unauthorized third parties to access consumer data. Website tracking practices, consent failures, pixel-based data sharing — those were CIPA problems, not CCPA problems.On March 27, 2026, the Northern District of California issued a ruling that dismantles that assumption. And if the trend it represents continues, the litigation exposure facing businesses that deploy third-party tracking technology without proper consent architecture just expanded substantially.
GET A FREE PRIVACY AUDIT TO SEE IF YOUR BUSINESS IS AT CCPA PRIVATE RIGHT OF ACTION LAWSUIT RISK
What Allison v. PHH Mortgage Actually Decided
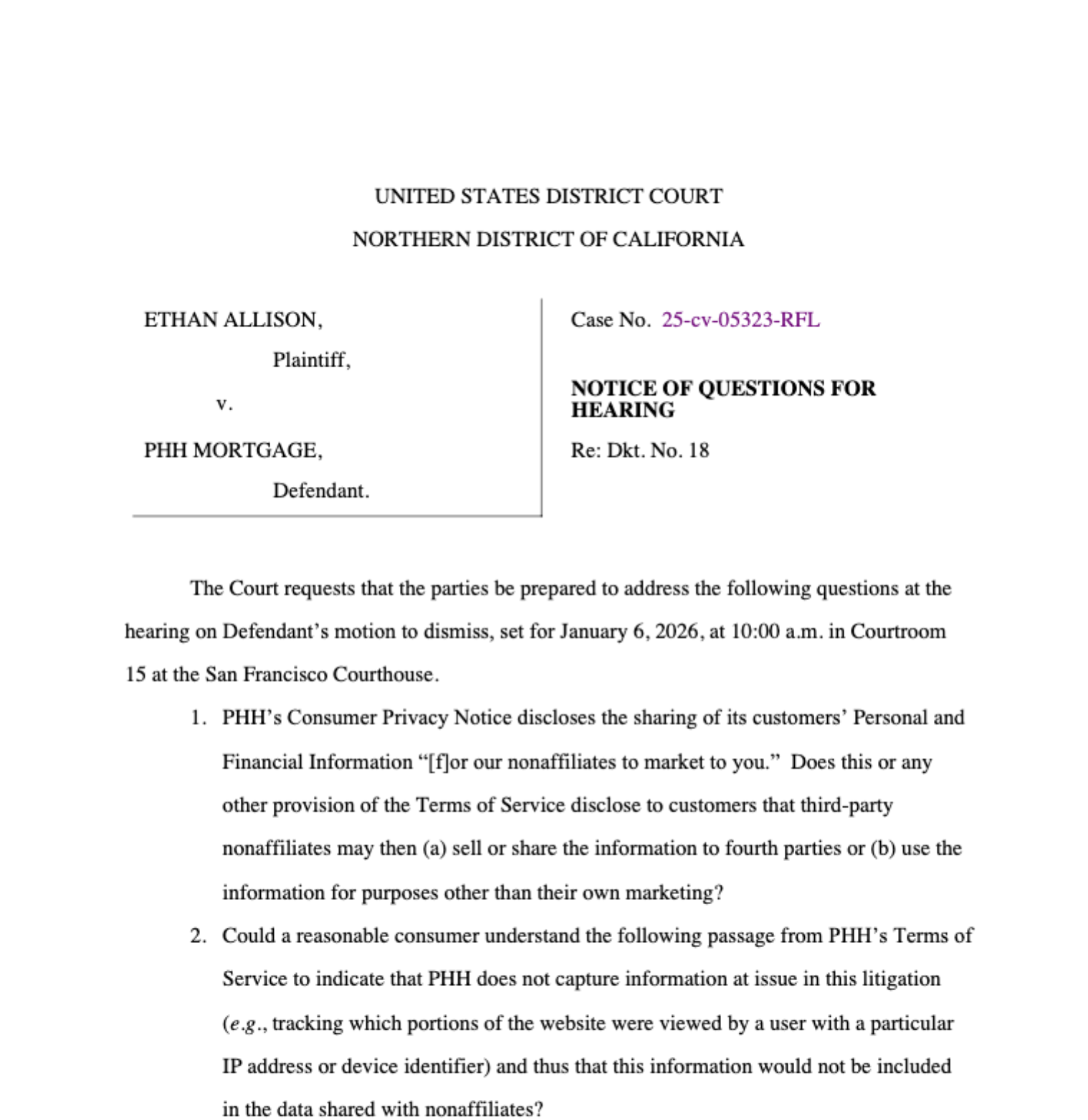
The “Data Breach Only” defense was possible until now. On the surface, Allison v. PHH Mortgage looks like a standard website tracking case — the kind that has been flooding California federal dockets for the past several years. The plaintiffs alleged that tracking technologies deployed on PHH Mortgage’s website disclosed users’ personal information to third parties without their knowledge or consent. The complaint included the expected cluster of claims: CIPA, the Electronic Communications Privacy Act, and related causes of action.
What made Allison different was the addition of a CCPA claim — and the court’s refusal to dismiss it.
PHH Mortgage moved to dismiss the CCPA cause of action on the theory that the statute’s private right of action is limited to traditional data breach scenarios. The Northern District rejected that argument, and did so with language that should command attention from every compliance and legal team in California.
The court held that “[n]othing in the plain language of the provision limits its application to data breaches by third parties.” Reading the text of California Civil Code § 1798.150 — the CCPA’s private right of action provision — the court found that the statute covers unauthorized disclosures of personal information regardless of whether the disclosure was intentional or negligent, and regardless of whether it was carried out by an external bad actor or by the business itself through its own systems and agents.
In other words: if your website is disclosing consumer personal information without authorization — through a tracking pixel that fires before consent is captured, through a session replay tool, through a third-party analytics tag that transmits data to an advertising platform — that may now be enough to trigger the CCPA’s private right of action. You don’t need a hacker. You don’t need a security incident. You need a plaintiff and an attorney who knows how to read your network request logs.
This Isn’t an Isolated Ruling
The Allison holding didn’t emerge from a vacuum. Two earlier cases pointed in the same direction.
In Shah v. Capital One Financial Corp., a court similarly declined to confine the CCPA’s private right of action to the traditional breach paradigm, finding that the statutory text supported a broader reading that could encompass privacy violations beyond unauthorized external access.
M.G. v. Therapymatch Inc. reached a comparable outcome, with the court applying the CCPA’s private right of action in a context that went beyond a conventional cybersecurity breach.
What Allison adds to this developing line of authority is something the earlier cases lacked: a more fully reasoned opinion that engages directly with the plain language of § 1798.150 and explains why the limiting construction PHH Mortgage advanced isn’t supported by the statute’s text. That reasoning makes Allison a more durable precedent and a more useful roadmap for plaintiffs’ counsel structuring future complaints.
The trend line across these three cases is not ambiguous. Courts in the Northern District of California are consistently rejecting the narrow reading, and they’re getting more articulate about why.
The Statute and Why This Reading Was Always Arguable
California Civil Code § 1798.150 provides a private right of action to consumers whose “nonencrypted and nonredacted personal information” is “subject to an unauthorized access and exfiltration, theft, or disclosure as a result of the business’s violation of the duty to implement and maintain reasonable security procedures and practices.”
The limiting construction that businesses have relied on focuses on the phrase “as a result of the business’s violation of the duty to implement and maintain reasonable security procedures” — reading that as a reference specifically to cybersecurity failures that allow external breaches. Under that reading, intentional data sharing practices, even if unauthorized, don’t trigger § 1798.150 because they aren’t the product of a security failure in the traditional sense.
What the Allison court rejected is the premise that this framing limits the statute to external breach scenarios. The duty to “implement and maintain reasonable security procedures and practices” — read more broadly — can encompass the obligation to implement consent mechanisms and data governance controls that prevent unauthorized disclosures. A company that deploys third-party tracking pixels without consent architecture, under this reading, may be failing its security and data governance obligations just as surely as one that left a database exposed to external access.
Whether that reading survives appellate review is an open question. But at the district court level in the Northern District, it is now the prevailing interpretation — and that’s where class action complaints get filed.
What This Means When You Stack CIPA and CCPA
Here is the practical consequence that matters most for businesses operating in California.
CIPA litigation based on tracking pixel claims has been accelerating for years, with plaintiffs arguing that third-party data collection scripts constitute unauthorized wiretapping under California Penal Code § 630 et seq. Those cases carry statutory damages of up to $5,000 per violation and have generated a substantial volume of class action filings — more than 3,000 data breach and privacy class actions were filed in 2025 alone, with CIPA-based pixel claims representing a meaningful portion of that volume.
What Allison opens up is the ability for plaintiffs to attach a CCPA claim to that same conduct. CCPA § 1798.150 provides for statutory damages between $100 and $750 per consumer per incident, or actual damages if greater, along with injunctive relief. On its own, those amounts may seem modest. But in a class action covering potentially thousands or millions of California website visitors, the aggregate exposure is substantial — and the combination of CIPA and CCPA claims in a single complaint creates both broader damages exposure and stronger settlement leverage.
The CIPA claim establishes the interception theory. The CCPA claim, post-Allison, establishes that the same conduct also constitutes an unauthorized disclosure of personal information by the business itself. Two theories, one set of facts, one tracking pixel that fired before a consent banner was acknowledged.
The Capability Test Problem, Compounded
Allison doesn’t exist in isolation from the other CIPA case law developing around third-party AI and analytics vendors. The “capability test” articulated in Taylor v. ConverseNow — which asks not whether a vendor did use call or session data for its own purposes, but whether it could — creates a parallel exposure vector that compounds the Allison problem.
Under the capability test, a company whose analytics or advertising vendor has contractual rights to access session data for any purpose (model training, quality improvement, internal research) carries CIPA exposure regardless of whether the vendor has exercised those rights. Under Allison‘s reading of the CCPA, that same data sharing arrangement may also constitute an unauthorized disclosure of personal information for CCPA purposes. The vendor agreement language that was previously just a CIPA concern is now potentially a CCPA concern as well.
What Needs to Change in Your Compliance Architecture
The Allison ruling compresses the urgency around several practices that compliance teams have sometimes treated as lower-priority items.
Consent architecture has to be technically enforced, not just disclosed. A privacy policy that mentions third-party advertising partners does not constitute consent to the specific data disclosures those partners receive. Under the Allison framework, the relevant question is whether the disclosure was authorized — and authorization requires a meaningful, contemporaneous consent mechanism, not a buried policy paragraph. If your tracking pixels fire before a consent event is logged, you have an authorization gap that a plaintiff’s attorney can now frame as both a CIPA violation and a CCPA violation.
Your vendor agreements need to be audited for capability exposure. Any contractual provision that grants a third-party vendor rights to access, retain, or use consumer data for the vendor’s own purposes — even operationally benign purposes like model improvement — creates the kind of unauthorized disclosure that Allison and the capability test cases are targeting. Those provisions need to be identified, negotiated, or disclosed to consumers with specificity.
The scope of “personal information” under the CCPA is broader than most implementations reflect. IP addresses, browser identifiers, session data, and behavioral signals can all qualify. If your consent flow was designed with the narrow breach reading of § 1798.150 in mind, it may not be capturing authorization for the full range of data your tracking stack is actually transmitting.
Documentation of consent events matters. In litigation, the burden will be on the business to demonstrate that consent was obtained before the relevant data disclosure occurred. That requires timestamped, auditable records of consent events tied to specific user sessions — not just a cookie banner that exists somewhere on the site.
The Dockets Are About to Get Busier
The Allison ruling was decided in late March 2026. Plaintiff’s firms that specialize in CIPA pixel cases have had several weeks to review the opinion and assess how to incorporate a CCPA count into their standard complaint architecture. The mechanics aren’t complicated — the same factual predicate that supports a CIPA wiretapping claim largely supports the Allison theory of CCPA liability. Adding the count requires additional pleading work, but the underlying investigation and the client identification process are identical.
What that means, practically, is that the existing pipeline of CIPA pixel cases — already running at historically high volumes — is likely to become a pipeline of CIPA-plus-CCPA cases in short order. Businesses that receive a demand letter or a complaint in the coming months should expect both.
The businesses that are best positioned to respond aren’t necessarily the ones with the most sophisticated consent platforms. They’re the ones that can produce clear, contemporaneous documentation showing that consent was obtained before disclosures occurred, that vendor agreements were reviewed and scoped, and that the organization made deliberate, documented decisions about its tracking architecture. That evidence — or its absence — will drive the early-stage motion practice and the settlement calculus in cases filed under the Allison framework.
If you made it this far reading our piece then know that the window to build that documentation before a claim arrives is now. Captain Compliance helps businesses audit their tracking architecture, close consent gaps, and produce the compliance records that matter when litigation is on the table.