Privacy risk is no longer a narrow compliance issue managed quietly in the background. It is a core business risk category that intersects with cybersecurity, legal exposure, customer trust, operational resilience, and revenue protection.
From a Chief Privacy Officer’s perspective, the real question is rarely whether the organization is technically “doing privacy.” The better question is whether the company has a clear, current, defensible understanding of how data is actually being collected, used, shared, retained, and governed across the business.
That distinction matters. Many companies believe they are in a strong position because their policies exist, their contracts are in place, and their teams can point to a completed compliance project from the past. But privacy risk does not stay still. Systems change. Vendors proliferate. Product teams ship faster. Marketing stacks evolve. Internal access grows quietly over time. What once looked controlled can drift into fragmentation without leadership realizing how far reality has moved from the original design.
That is why sophisticated privacy programs do not start with assumptions, reactive remediation, or the purchase of another tool. They start with a Privacy & Data Risk Health Check: a structured diagnostic that gives leadership a real-world view of present-state exposure, control maturity, and operational gaps.
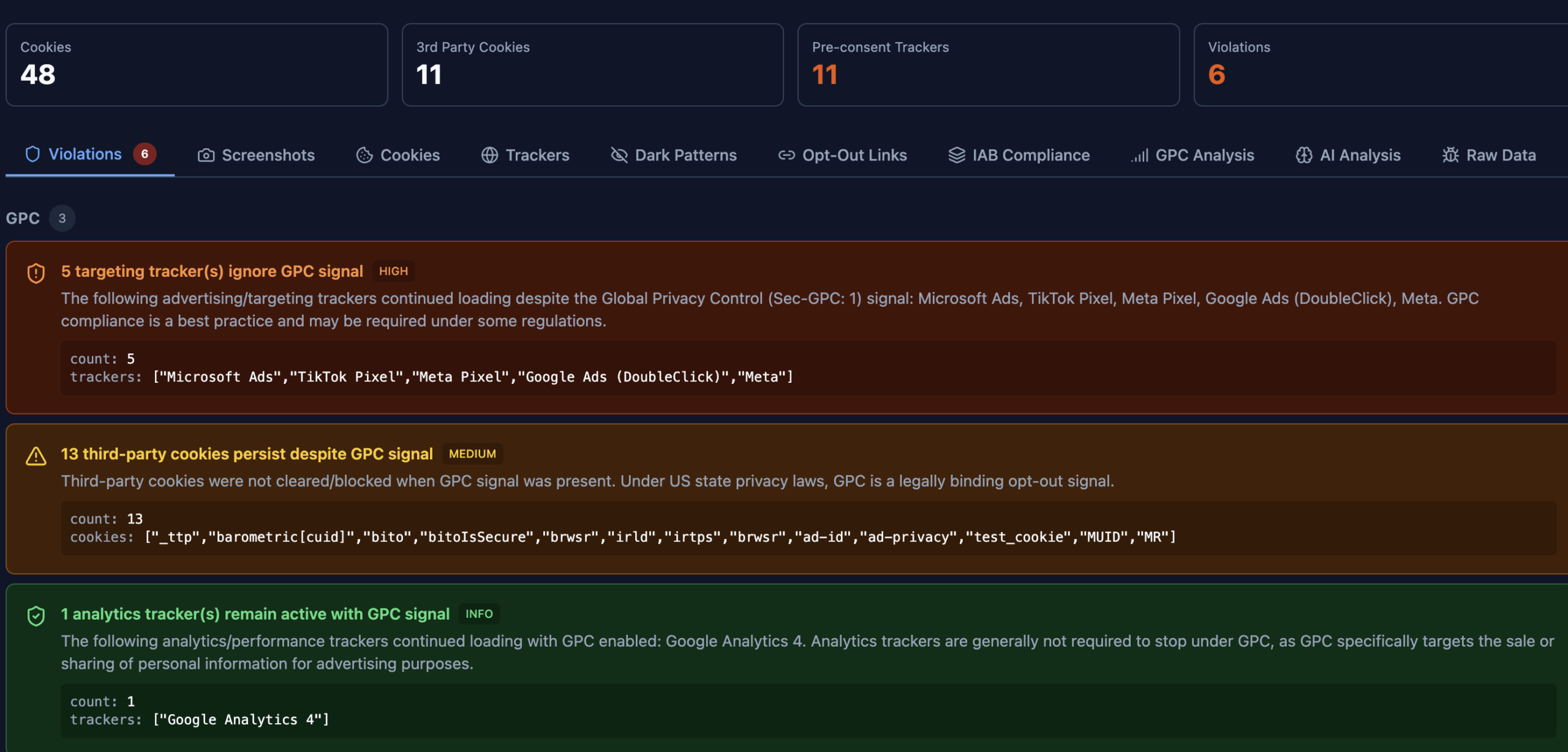
For the modern Chief Privacy Officer, a Health Check is not a formality. It is the starting point for disciplined governance, more credible executive reporting, and better risk-adjusted decision-making. The Captain Compliance radar tool monitors and keeps businesses up to date with their compliance and reports when something is out of compliance violating privacy frameworks.
Why Assumptions Are Dangerous in Privacy Governance
One of the most common weaknesses in privacy programs is assumed compliance. Leadership teams often assume consent is functioning correctly, assume data inventories are reasonably complete, assume access controls are appropriately scoped, and assume vendors are being monitored with enough rigor. In practice, those assumptions are often based on stale documentation, partial visibility, or a compliance exercise that reflected a moment in time rather than the current state of the environment.
For a Chief Privacy Officer, assumption is not just an operational weakness. It is a governance liability.
First, assumptions create a false sense of assurance at the executive and board level. A board may hear that the organization has a privacy framework, but that statement means very little if leadership cannot show whether controls are operating consistently in the live environment.
Second, assumptions create drift between policy and practice. The policy may say one thing, the data flow map may show another, and the production stack may behave in a third way entirely. This is especially common in fast-moving organizations where engineering, sales, product, and marketing each introduce new systems or workflows without a unified data governance discipline.
Third, assumptions allow liability to build quietly. Privacy failures rarely arrive all at once. They usually emerge through the accumulation of small issues: an outdated vendor contract, a stale admin account, a tracking technology misfire, an undocumented data transfer, an unreviewed retention setting, or a rights-request workflow that works on paper but breaks under real volume.
A Privacy & Data Risk Health Check replaces those assumptions with evidence. It helps the CPO answer one of the most important executive questions in privacy management: What is actually true today?
What a Privacy & Data Risk Health Check Delivers
A well-run Health Check is not a checklist exercise and it should not be treated like a lightweight audit. From a CPO’s perspective, it is a structured, enterprise-level diagnostic that establishes ground truth across governance, data flows, systems, access, vendor dependencies, and execution maturity.
At a minimum, it delivers three categories of value immediately.
A Defensible View of Exposure
The first job of a privacy leader is to understand where the enterprise is exposed in real terms, not theoretical ones. A Health Check gives leadership visibility into where sensitive data sits, how it moves, which teams and vendors can access it, whether user choice signals are honored, and which controls are inconsistent, outdated, or missing altogether.
This is the difference between abstract compliance and operational truth. A policy may claim data minimization, but the Health Check may reveal duplicate storage across business units. A consent framework may appear sufficient, but the Health Check may uncover downstream technologies acting outside the intended preferences model. A vendor inventory may look complete, but the Health Check may identify shadow tools or legacy processors still touching data.
For the CPO, that visibility creates defensibility. It turns privacy from a collection of assumptions and scattered artifacts into a coherent risk picture that can be discussed with the General Counsel, CISO, CFO, CEO, audit committee, or board with confidence.
A Prioritized Action Roadmap
Privacy leaders rarely struggle because they have nothing to fix. They struggle because there is too much to fix and not enough time, headcount, or budget to address every issue simultaneously. A strong Health Check solves this by organizing findings into a prioritized roadmap based on business impact, regulatory significance, exploitability, and implementation feasibility.
That roadmap allows the CPO to distinguish between matters that are urgent, matters that are important, and matters that can be sequenced later without materially increasing risk. It also helps prevent one of the most common privacy-program mistakes: spending meaningful resources on visible but low-value work while more serious issues remain unresolved.
Boards and executive teams increasingly expect prioritization logic, not just activity. A Health Check gives the CPO a disciplined framework for showing why certain issues should be addressed now, why others can be deferred, and what level of residual risk the business is choosing to carry in the interim.
Cross-Functional Alignment
Privacy risk is not owned by one department. It is distributed across engineering, security, legal, product, procurement, marketing, data analytics, and customer operations. As a result, even strong privacy leaders can fail if the rest of the enterprise is working from inconsistent assumptions or fragmented information.
A Health Check helps create a shared operating picture. It clarifies ownership. It surfaces hidden dependencies. It shows where handoffs are failing and where decision rights are ambiguous. Instead of privacy being viewed as a blocker or an isolated compliance function, it becomes a coordinating force that helps the enterprise execute with more discipline and less confusion.
For a CPO, this is one of the most underrated benefits. Better alignment reduces friction, accelerates remediation, and improves the quality of executive reporting because the underlying facts are no longer siloed.
Why Health Checks Lower the Total Cost of Risk
From a board and executive perspective, privacy is increasingly evaluated through a cost-of-risk lens. The question is not just whether something is compliant, but whether the organization is allocating resources intelligently to reduce financial, operational, and reputational exposure.
A Privacy & Data Risk Health Check helps answer that question in a practical way.
It Enables Earlier Intervention
The earlier a privacy issue is identified, the cheaper it is to address. Misconfigured tools, overbroad access rights, retention failures, or incomplete vendor controls are materially easier to correct before they evolve into complaints, incidents, investigations, litigation, or public trust failures.
Health Checks allow the organization to intervene before the cost curve steepens. That can mean avoiding rushed remediation projects, outside counsel escalation, emergency engineering work, or commercially damaging customer fallout.
It Reduces Wasteful Spending
Many organizations buy privacy-related tools before fully understanding what problem they are trying to solve. The result is duplicate platforms, underused features, poor implementations, and systems that create noise rather than clarity.
A Health Check allows the CPO and executive team to evaluate which investments are actually reducing risk and which are simply creating the appearance of maturity. It becomes easier to justify strategic spend when the company can tie budget to identified gaps, measured exposure, and clearly prioritized remediation goals.
It Improves Operational Execution
Ambiguity is expensive. When ownership is unclear, when workflows are inconsistently followed, and when different teams maintain different versions of the truth, the business incurs hidden costs through delay, rework, duplication, and control failure.
Health Checks reduce this drag by clarifying who owns what, how work should move, where escalation should happen, and which risks require executive attention. The result is not only a stronger privacy program, but also a more efficient operating model.
What Mature CPOs Look For in a Health Check
From an executive privacy standpoint, not all Health Checks are equally useful. A mature CPO will want the exercise to move beyond surface-level compliance review and focus on the areas most likely to create material exposure or governance weakness.
That typically includes:
- Whether the organization has an accurate, current understanding of its data flows and processing activities
- Whether consent, notice, and preference mechanisms align with actual downstream system behavior
- Whether high-risk data categories are subject to enhanced governance and appropriate controls
- Whether third-party vendors are governed proportionately to the sensitivity and volume of data involved
- Whether user rights workflows are scalable, documented, and capable of standing up to regulatory scrutiny
- Whether access rights, retention settings, and internal data handling practices reflect least-privilege and minimization principles
- Whether privacy governance is integrated with legal, security, product, and procurement decision-making
- Whether leadership can translate findings into board-ready reporting and a realistic remediation roadmap
CPO Checklist: What to Review Before and After a Privacy & Data Risk Health Check
For Chief Privacy Officers, the value of a Health Check is directly tied to preparation and follow-through. The checklist below can be used as a practical executive guide.
Before the Health Check
- Confirm the scope of the review, including business units, systems, vendors, products, and jurisdictions
- Identify whether the objective is baseline visibility, remediation planning, board reporting, regulatory readiness, or all of the above
- Gather current privacy policies, notices, data maps, vendor lists, retention standards, and incident or complaint history
- Document key stakeholders across legal, security, IT, product, marketing, procurement, and operations
- Clarify which data categories are highest risk, including sensitive personal information, employee data, children’s data, financial data, and regulated-sector data
- Identify any known pain points such as DSAR delays, consent inconsistencies, vendor sprawl, or unclear system ownership
- Determine how findings will be escalated and who will approve remediation priorities
During the Health Check
- Validate whether documented data flows match real operational behavior
- Test high-risk controls rather than relying solely on policy statements or screenshots
- Look for evidence of control drift, shadow processing, stale access, or inconsistent retention practices
- Evaluate privacy obligations in the context of actual business processes, not idealized workflows
- Press for practical remediation paths, not just observations or abstract risk statements
- Separate immediate issues from medium-term program improvements
After the Health Check
- Translate findings into a risk-ranked action plan with owners, deadlines, and dependencies
- Escalate material issues to executive leadership with a clear explanation of business and regulatory impact
- Align remediation sequencing to budget, internal capacity, and enterprise priorities
- Update governance documentation, policies, and workflows based on validated findings
- Establish a cadence for reassessment, especially after major product, vendor, or systems changes
- Incorporate results into board and audit committee reporting
- Measure progress over time so privacy maturity is tracked as an operational discipline, not a one-time project
Board Reporting Template: Privacy & Data Risk Health Check Summary
One of the most valuable outputs of a Health Check is better executive and board communication. The template below is structured for board packets, audit committee summaries, or executive risk reviews.
1. Executive Summary
Objective: Provide a concise overview of the purpose of the Health Check, the scope reviewed, and the high-level conclusion regarding current privacy and data risk posture.
Suggested language: The organization completed a Privacy & Data Risk Health Check to assess current-state exposure, control effectiveness, and governance maturity across key systems, workflows, and third-party relationships. The review identified a mix of strengths, moderate gaps, and priority issues requiring near-term remediation.
2. Scope of Review
- Business units reviewed
- Jurisdictions covered
- Systems and data environments examined
- Third-party/vendor categories assessed
- Control areas tested (e.g., consent, access, retention, rights response, vendor governance)
3. Top Findings
| Finding | Risk Level | Business Impact | Recommended Action | Owner | Target Date |
|---|---|---|---|---|---|
| [Example: Incomplete data flow documentation across marketing stack] | High | Limits consent defensibility and creates notice accuracy concerns | Reconcile systems, update data maps, validate downstream tags and vendor flows | CPO / Marketing Ops / Engineering | [Insert date] |
| [Example: Overbroad internal access to customer data] | High | Increases misuse, insider risk, and regulatory exposure | Implement role review, least-privilege remediation, and quarterly access attestations | CISO / IT / Data Owner | [Insert date] |
| [Example: Inconsistent retention settings across legacy tools] | Medium | Creates minimization and storage limitation risk | Standardize schedules and align systems to approved retention rules | Privacy / Legal / IT | [Insert date] |
4. Risk Posture Summary
| Category | Status | Commentary |
|---|---|---|
| Data Visibility | [Red / Amber / Green] | [Brief assessment] |
| Consent & Notice Integrity | [Red / Amber / Green] | [Brief assessment] |
| Vendor Governance | [Red / Amber / Green] | [Brief assessment] |
| Access Governance | [Red / Amber / Green] | [Brief assessment] |
| Data Subject Rights Readiness | [Red / Amber / Green] | [Brief assessment] |
| Retention & Minimization | [Red / Amber / Green] | [Brief assessment] |
| Overall Program Maturity | [Red / Amber / Green] | [Brief assessment] |
5. Management Action Plan
Immediate actions (0–30 days): List critical remediation items, temporary controls, and executive escalations.
Near-term actions (30–90 days): List operational fixes, vendor reviews, system updates, and control enhancements.
Longer-term actions (90+ days): List program maturity initiatives, tooling optimization, governance enhancements, and recurring measurement.
6. Decisions or Support Requested from the Board
- Approval for budget or headcount tied to priority remediation
- Support for enterprise-wide governance expectations across business units
- Acknowledgment of residual risk in deferred areas
- Direction on reporting cadence and materiality thresholds
What Happens Next After the Data Privacy Health Check?
A key strength of beginning with a Health Check is that it creates optionality. It gives leadership a baseline without forcing the organization into a single rigid next step.
Some companies will move quickly to address the most acute issues. Others will use the findings to support a broader privacy transformation program. Still others will adopt the Health Check as a recurring benchmark, measuring improvement over time and reassessing after major product launches, acquisitions, system migrations, or new regulatory developments.
From the CPO’s perspective, all of these paths can be valid. What matters is that the next move is based on visibility, not guesswork.
Why Clarity Is a Strategic Advantage
For Chief Privacy Officers, progress without clarity is not speed. It is exposure.
The organizations with the most resilient privacy programs are not necessarily the ones with the longest policy binders or the most software. They are the ones that understand their actual data environment, know where their meaningful risks sit, and can translate that reality into prioritized action and credible executive reporting.
A Privacy & Data Risk Health Check creates that foundation. It replaces assumption with evidence, fragmentation with alignment, and reactive remediation with risk-informed leadership.
That is why mature privacy teams begin there. Not because it is cautious, but because it is strategic.