California’s Anti-Hacking Law Is Now a Privacy Weapon — And Ad Tech Is in the Crosshairs. This is the story on how CDAFA and California’s Privacy Statutes Are Reshaping Data Liability for the Ad Retargeting Industry.
The Law Nobody Expected to Matter
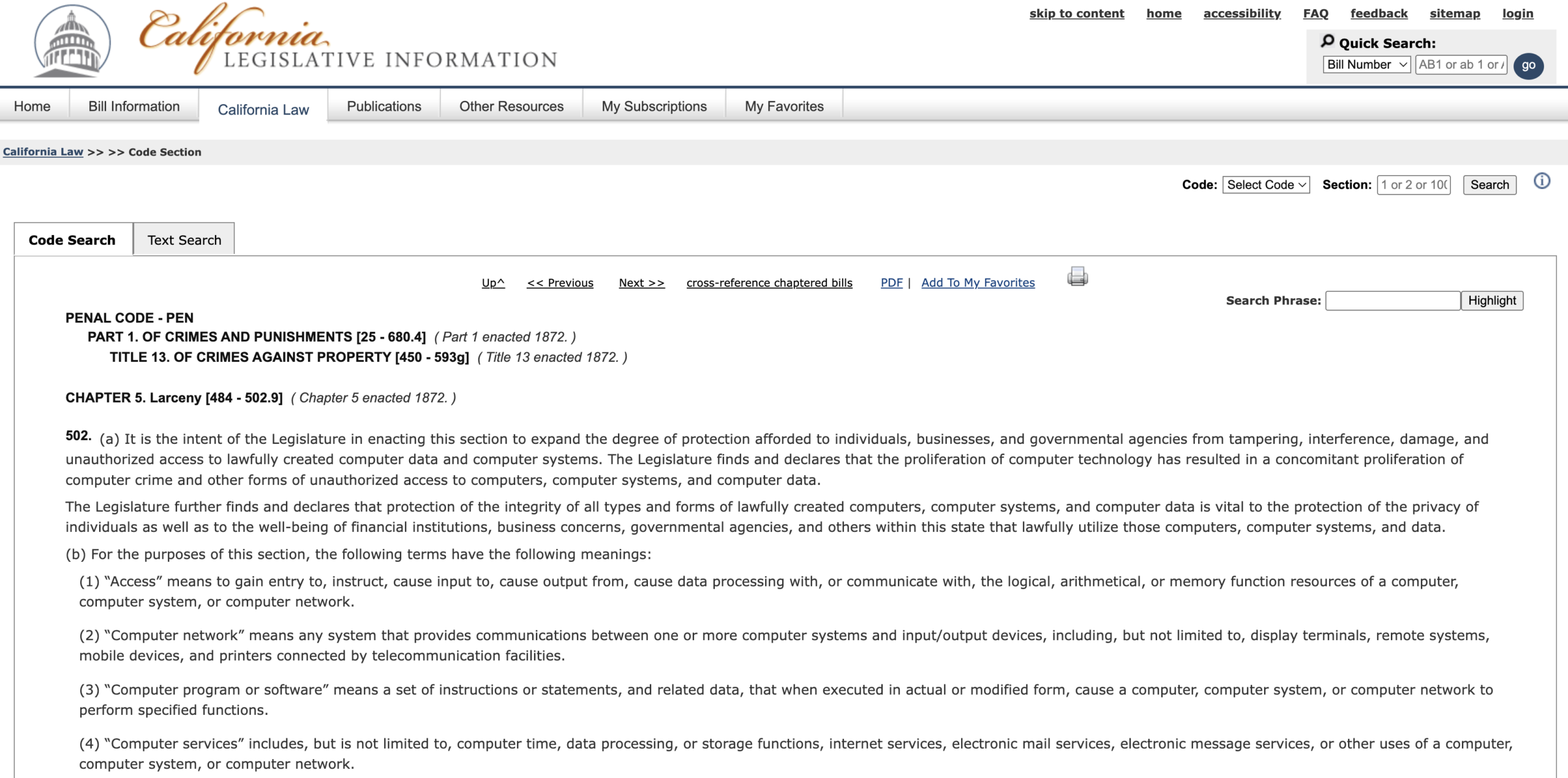
When California enacted the Computer Data Access and Fraud Act — Cal. Penal Code § 502, widely known as CDAFA (and sometimes referenced as CCCDAFA, the California Comprehensive Computer Data Access and Fraud Act) — it was designed to go after hackers. It was an anti-intrusion statute, a tool for prosecuting people who broke into computer systems without authorization. Nobody was really thinking about ad pixels.
That was then. Today, CDAFA sits at the center of one of the most rapidly expanding categories of California privacy class action litigation, and the defendants aren’t hackers — they’re some of the most recognizable companies in the world. Meta, TikTok, healthcare providers, retailers, streaming services, and virtually any business that ever dropped a tracking pixel on a webpage is now potentially exposed.
The statute didn’t change. The internet did. And plaintiffs’ lawyers noticed and boy are they taking advantage of this “breach” of trust between businesses and consumers or at least alleged breach as they target businesses over these laws.
What the CDAFA Actually Says
The operative provision in most of these cases is § 502(c)(7), which prohibits “causing to be accessed” any computer, computer system, or computer network without permission. That “caused to be accessed” language has become one of the most actively litigated provisions in modern privacy lawsuits, particularly in cases involving third-party tracking technologies and pixel-based data transmission. Its breadth reflects a legislative intent that the statute reach not only direct unauthorized access but conduct that causes or enables access by others — and that formulation, courts have found, can fit pixel deployment with uncomfortable precision.
The civil enforcement hook is § 502(e). Any person who suffers damage or loss by reason of a violation may bring a civil action for compensatory damages, injunctive relief, and — critically — attorney’s fees in the court’s discretion. Unlike federal computer access statutes, CDAFA carries no minimum damage threshold for civil claims. That last point matters enormously. No minimum damage floor means class actions can proceed even when individual harms are hard to quantify — which is almost always the case in ad tracking litigation.
What a Tracking Pixel Actually Does (and Why It Creates Legal Risk)
A “pixel” is used for tracking user behavior and collecting data about users’ interactions with website content. The mechanics, while technically straightforward, are legally loaded.
Take the Meta Pixel as the canonical example. Third-party web developers can install Meta Pixels on their websites. The Meta Pixel contains small amounts of JavaScript code that loads a library of functions that developers can use to track actions users take on their sites. These user actions are logged and sent to Meta, where developers can use and analyze the data. Meta then attempts to match the data to one of its users. The data collected through the Meta Pixel, as well as matched with data Meta already has on users, can be used for advertising activity.
The TikTok Pixel operates on the same general principle — scripts running on a defendant’s website send visitor details to TikTok, including browser information, geographic information, referral tracking, and URL tracking. Crucially, the collection occurs when the visitor lands on the website page, regardless of whether the visitor interacted with any cookie banner.
From a user perspective, nothing visible happens. From a legal theory perspective, that invisibility is precisely the problem plaintiffs allege: your device was accessed, your data was extracted, your browsing behavior was packaged and transmitted — and you had no idea.
The Legal Arsenal: CDAFA Is Just One Piece
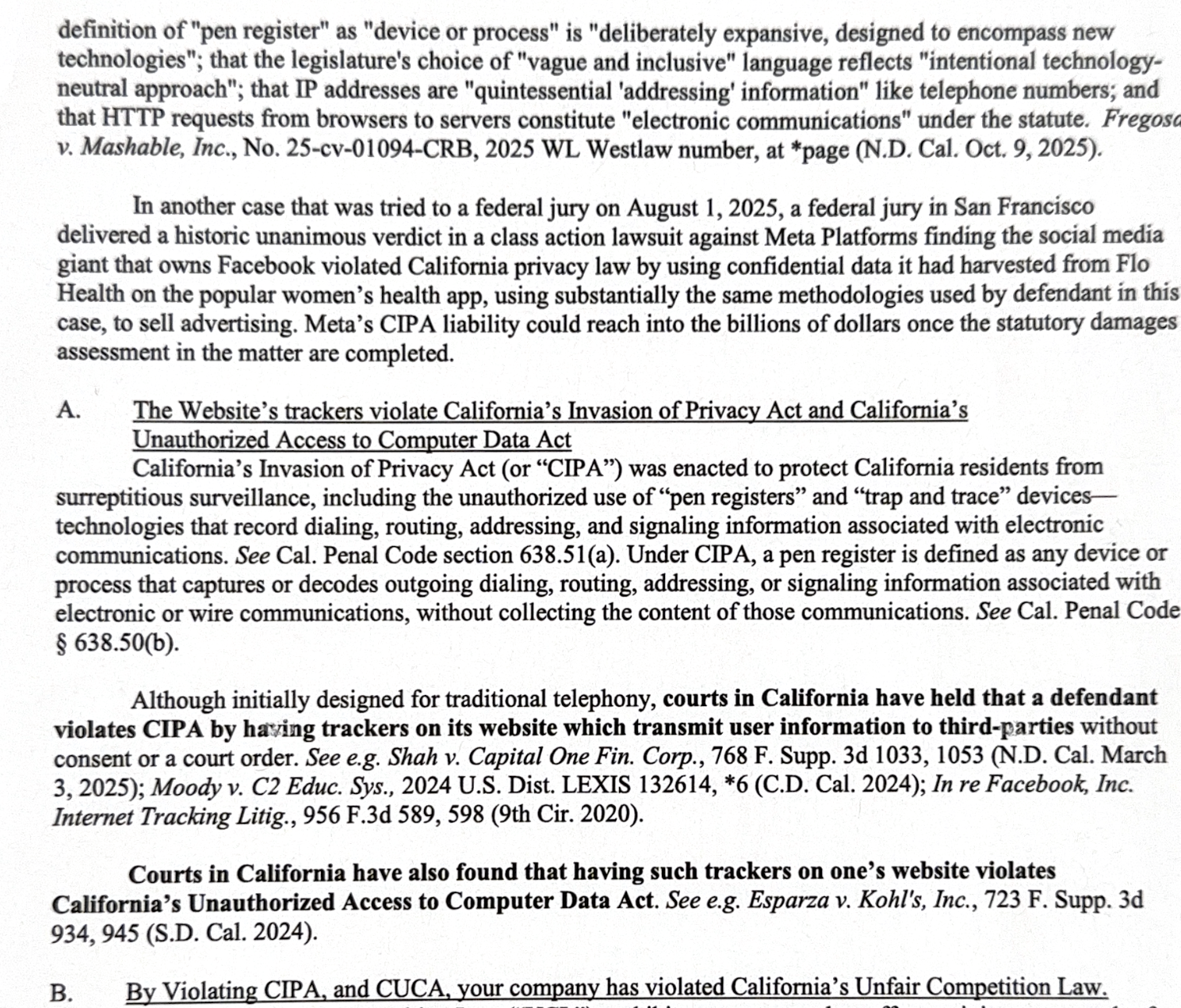
CDAFA doesn’t operate in isolation. Privacy plaintiffs building these cases typically layer multiple California statutes, and understanding how they interact is essential to understanding the litigation landscape.
CIPA (California Invasion of Privacy Act, §§ 631 and 638.51) is typically the lead claim. In the latest trend in California class action litigation, plaintiffs are invoking CIPA’s “wiretapping” (Section 631) and “pen register” (Section 638.51) prohibitions to assert invasion of privacy claims against businesses using solutions like pixels, plugins, or cookies on their websites to track visitors. Common targets include tools like the Meta Pixel and TikTok Pixel, as well as many other tracking and advertising technologies.
CDAFA typically rides alongside as a secondary claim, with the theory being that the pixel code, by executing on a user’s device and transmitting data outward, constitutes unauthorized access to the user’s computer.
CCPA (California Consumer Privacy Act) adds another layer. In 2024, courts were particularly receptive to web tracking challenges brought under CIPA, and the CCPA has been expanded in ways that make pixel-based data collection increasingly actionable. The definition of “sensitive personal information” in the CCPA was amended to include consumers’ neural data and to specify that “personal information” can exist in various formats, such as abstract digital formats — amendments that went into effect on January 1, 2025.
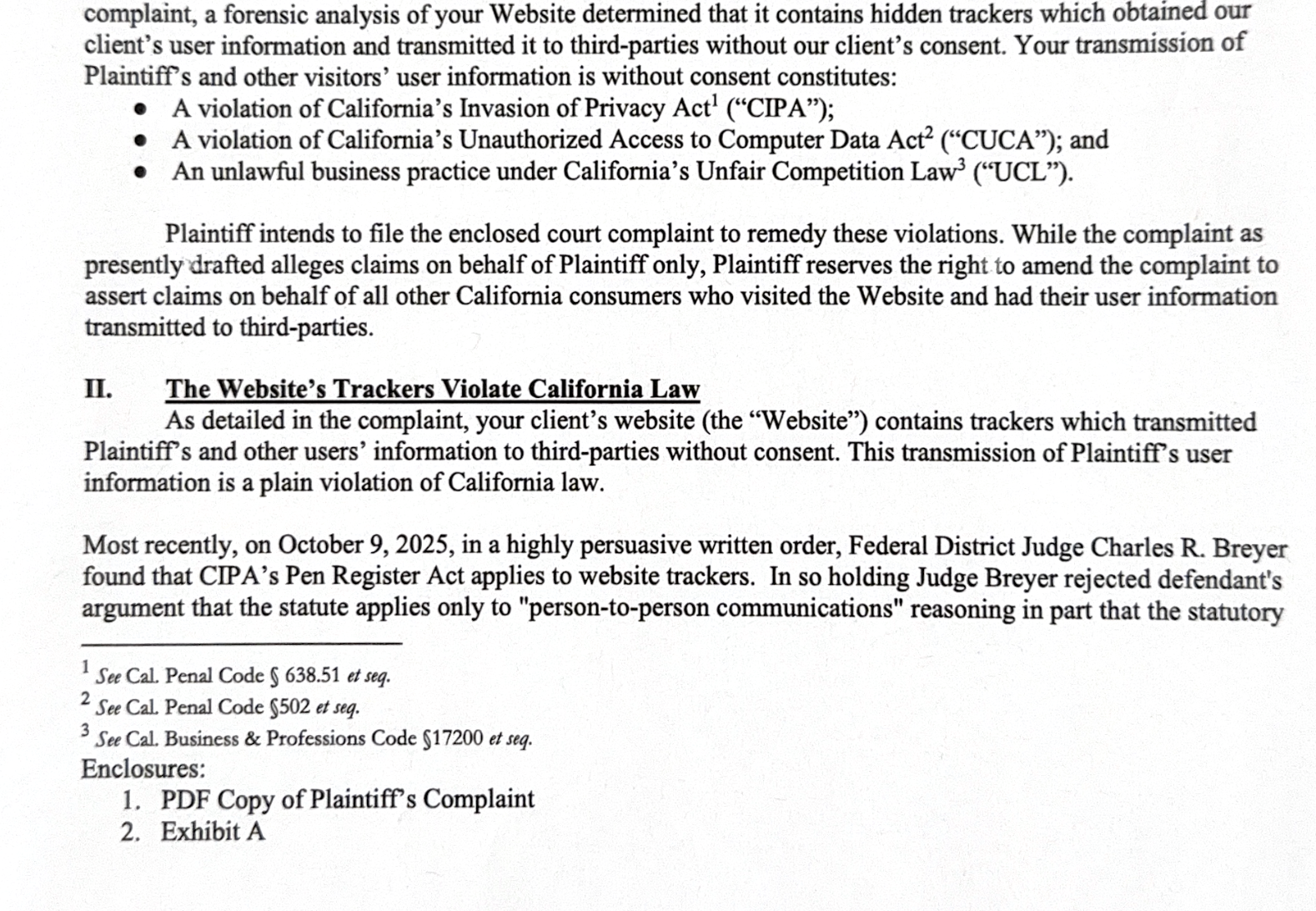
Here is an example of a complaint we found from a law firm alleging violations of California’s Invasion of Privacy Act; Unauthorized Access to Computer Data Act; and Unfair Competition Law.
The Landmark Cases Shaping the Battlefield
In re Meta Pixel Healthcare Litigation is arguably the most significant case in this space. Consumers claim that Meta’s proprietary Meta Pixel tool intercepts and transmits protected patient health information to Meta Platforms for advertising purposes on Facebook and Instagram in violation of state and federal consumer protection laws, including invasion of privacy, CDAFA, and the Electronic Communications Privacy Act (ECPA). Through its account managers and representatives, Meta is allegedly aware that it is receiving patient data from hundreds of different medical providers in the United States without patient knowledge, consent, or valid HIPAA authorizations.
The scale of the alleged breach is staggering. Through experts, plaintiffs have identified at least 664 hospital systems or medical provider web properties where Meta has received patient data via the Meta Pixel. And the court has allowed the case to proceed — on January 29, 2024, the court rejected Meta’s argument that patients’ privacy claims are foreclosed because their communications may have been conducted via publicly available webpages. Plaintiffs can move forward with claims of invasion of privacy/intrusion on seclusion, CDAFA, and trespass to chattels.
GoodRx showed what a settlement in this space looks like. The November 2023 approval of a $13,000,000 classwide settlement in Hodges v. GoodRX Holdings is notable. Plaintiffs alleged that the use of various pixels and SDKs on GoodRx’s website violated state and federal wiretapping statutes, consumer protection laws, and common law privacy rights by intercepting user data and sharing it with vendors without users’ consent.
Camplisson v. Adidas is one of the most recent cases fueling alarm among businesses. A Southern District of California judge ruled that common website tracking tools like the TikTok Pixel and Microsoft Bing trackers may violate California’s wiretapping law, even when they’re doing exactly what thousands of businesses use them for every day. The Adidas ruling rejected both of the company’s core defenses: the judge relied on what the court called CIPA’s “intentionally broad language” and found that limiting pen registers only to processes that collect all information would undermine CIPA’s privacy protection purpose.
The Consent Problem — And Why Footer Privacy Policies Don’t Fully Protect You
One of the most important practical takeaways from this litigation wave is that standard website privacy practices are no longer adequate consent mechanisms. The Adidas case made this explicit. The court found two flaws in Adidas’s consent mechanism: the terms and privacy policy weren’t sufficiently conspicuous — visitors had to scroll down to the footer to find them — and there was no pop-up window or similar method requiring visitors to affirmatively demonstrate their agreement. Historically, people placed terms of service and privacy policies in the footer of their websites, but California courts have ruled that such terms are not enforceable unless they are part of a clickwrap agreement.
This is a significant shift. Businesses that believed a privacy policy disclosing pixel use was sufficient protection are discovering that California courts may require affirmative, conspicuous consent — not passive disclosure buried in footer links.
There’s also the timing problem: some courts have found that data collection occurs when the visitor lands on the website page, regardless of the cookie banner — meaning a cookie consent popup that appears after page load may be too late to provide legally meaningful consent for data that’s already been transmitted.
The Courts Are Divided — and Frustrated
The judicial landscape on these issues is genuinely unsettled, and some courts have begun expressing open frustration with how the litigation is evolving.
Several courts pushed back in 2025 with defendant-friendly rulings that dismissed CIPA claims outright — including Price v. Headspace, Kishnani v. Royal Caribbean Cruises, Mitchener v. Talkspace, and Mitchener v. CuriosityStream. All four of these decisions held that the TikTok Pixel does not fall within CIPA § 638.51’s scope.
But in the Eating Recovery Center case, a California federal court that ultimately granted summary judgment for the defendant did so while issuing a remarkable statement about the state of the law. The court emphasized that it was “virtually impossible” to apply CIPA to internet communications and urged the California legislature to “step up” and “speak clearly” about how internet activity should be treated under the statute in light of a deluge of claims that have been filed recently against website operators.
That call for legislative clarity reflects a real tension: courts are being asked to apply mid-twentieth-century wiretapping and computer access statutes to technologies their drafters couldn’t have imagined, and the results are inconsistent.
The CDAFA’s Specific Problem in Court: What Counts as “Property”?
One recurring issue specific to CDAFA in the pixel context is that courts have sometimes narrowed its reach in ways that CIPA doesn’t face. In at least one ruling, a motion to dismiss was granted on CDAFA and UCL violations on the basis that personal information did not constitute “property” for the purposes of CDAFA — while CIPA and CCPA claims were allowed to proceed.
This means CDAFA, while powerful in theory, doesn’t always survive as a standalone claim in pixel cases. Plaintiffs use it as part of a multi-statute stack precisely because any single theory may be dismissed while others proceed — the redundancy is a feature, not a bug, of the litigation strategy.
Class Certification: Where the Real Fight Happens
The central legal questions of whether the access was “without permission” and whether the statutory elements are satisfied do not vary by individual class member, which means that a single adjudication resolves liability as to the entire class. That’s the plaintiffs’ key advantage — they can certify massive classes because the legal question is common to everyone who visited a given website.
The defense response has focused on the damages side. Defendants routinely press the argument that calculating each class member’s share of damages requires individualized inquiry that defeats predominance on the damages side even where liability is common.
The settlement pressure this creates is enormous. That prospect intensifies settlement pressure and has contributed to the frequency with which CDAFA privacy lawsuits in the pixel and tracking context resolve through substantial class settlements rather than proceeding to judgment. Defense counsel in CDAFA class actions should factor the fee-shifting exposure into settlement authority calculations at every stage of litigation, because the fees tail can be as significant as the damages exposure in well-pleaded class cases.
California’s Unauthorized Access to Computer Data Act: How an Anti-Hacking Law Became Ad Tech’s Biggest Legal Threat
The litigation wave isn’t subsiding. 2024 saw more cases in more states against healthcare entities challenging their use of pixel technology on their websites, and creative theories raised under different state privacy and wiretapping laws are continuing to emerge.
For any business operating a consumer-facing website — particularly in healthcare, financial services, or e-commerce — the minimum steps include:
Audit your pixel stack. Know every third-party tracking tag running on your site, what data it collects, and where that data goes. Many businesses inherit pixels from previous developers or marketing vendors without full visibility into what’s actually firing.
Upgrade your consent mechanism. Footer privacy policies are no longer adequate in California. Clickwrap agreements, conspicuous consent banners, and affirmative opt-in mechanisms for tracking are increasingly required — not just best practices.
Watch the timing of data collection. If your cookie banner appears after page load, data may already be transmitting. Configure your tag management to fire tracking pixels only after affirmative consent is recorded.
Map your HIPAA exposure separately. Healthcare entities face a compounded risk. The Meta Pixel Healthcare Litigation demonstrates that CDAFA exposure in medical contexts is bundled with HIPAA liability and ECPA exposure — a combination that makes settlement values significantly higher.
Monitor the legislative response. With courts openly calling on the California Legislature to clarify CIPA’s application to internet communications, statutory amendments are possible. Any change to how consent, “contents,” or “pen register” are defined could shift the litigation landscape dramatically.
California Unauthorized Access to Computer Data Act Is Now a Privacy Lawsuit Machine — And Ad Pixels Are the Target
What’s happening here is a slow-motion legal reckoning with the infrastructure of digital advertising. The Meta Pixel, the TikTok Pixel, and hundreds of similar tools were built and deployed at scale because they worked — they enabled precise retargeting, conversion tracking, and audience matching that made digital advertising extraordinarily effective. The business case was clear, the legal risk seemed manageable, and compliance teams weren’t flagging old anti-hacking statutes as material concerns.
That calculus has changed. California’s suite of privacy and computer access laws — CIPA, CDAFA, and CCPA — has been retooled by plaintiffs’ lawyers into a formidable liability framework, and courts, while divided, have allowed enough of these cases to survive to keep the pressure on. The $13 million GoodRx settlement won’t be the last of its kind. The Meta pixel healthcare case — with 664 hospital systems implicated — could produce something much larger.
The question for businesses is no longer whether to take ad pixel liability seriously. It’s how fast they can audit, remediate, and restructure their consent practices before the next demand letter arrives.